Microsoft announces cloud 9sin innovation to simplify security, compliance, and identity
2020 will be remembered as a year of historic transformation. The pandemic has changed the way businesses operate and people work. One thing that has not changed is our basic human nature and the need to feel safe. Being safe and feeling safe is what allows us to do more, create more, and have trust in the technology that connects us all.
It’s no wonder, then, that cyber-security is so important right now. Digital security is about people—
All of this takes place against a backdrop of advanced threats and adversaries. For example, Microsoft threat intelligence teams recently exposed cyberattackstargeting people and organizations involved in the upcoming U.S. presidential election including unsuccessful attacks on people associated with both presidential campaigns from a variety of foreign activity groups known to Microsoft as Strontium, Zirconium, and Phosphorus.
For those responsible for securing their organization’s digital infrastructure, this has all come on top of what they were already navigating—
Countless innovative companies like ASOS, CenturyLink, Erie Insurance, Frost Bank, Rabobank, Unilever, Rockefeller Capital Management, Uniper, Komatsu, and The Little Potato Company; and public sector organizations including the US Department of Defense, New Jersey Administrative Office of the Courts, Ashford & St. Peter’s Hospitals (NHS), St. Luke’s, and Durham University are tapping into the Microsoft cloud to help secure their futures. Today we’re delivering a new set of security, compliance, and identity innovations to help all customers simplify and modernize their environments by embracing the reality that the past seven months have likely reshaped the next 10 years of security and digital transformation.
Modern security with a new Microsoft Defender
Poor security posture is often rooted in complexity. Security teams have historically struggled to keep up with threats and signals across a patchwork of poorly integrated solutions that fail to cover the breadth of workloads, clouds, and devices that businesses run on. Fortunately, the cloud has given rise to a new generation of modern security tools that simplify the defender experience by combining signals and automating responses to catch threats that would otherwise go unchecked. The most important emerging tools are Extended Detection and Response (XDR) and cloud-native Security Information & Event Management (SIEM). Most vendors only offer one or the other.
Microsoft offers a unique approach that empowers security professionals with both cloud-native SIEM and XDR tools from a single vendor. This brings a new level of integration that gives defenders the best of both worlds—
Today we are making the following announcements to simplify the defender experience with modern and integrated capabilities:
- We are unifying all of our XDR capabilities together and rebranding them as Microsoft Defender, inclusive of Microsoft 365Defender and Azure Defender.
- Microsoft Defender offers the broadest resource coverage of any XDR in the industry, spanning identities, endpoints, cloud apps, email and docs, infrastructure, and cloud platforms.
- Microsoft Defender uses powerful workflows and AI to correlate alerts across attack vectors, provide an end-to-end view of the attack, and automatically heal affected assets.
In addition to bringing our XDR together under Microsoft Defender, we are also announcing new Defender capabilities:
- Microsoft Defender for Endpoint is now available for all major platforms, with the general availability of protection for Android devices and a preview for iOS.

- Azure Defender has a new unified dashboard experience within Azure Security Center that gives you visibility into your alerts and which resources are currently monitored.
- Azure Defender has new protections for SQL on-premises, Azure Kubernetes, Azure Key Vault, and IoT.
- Azure Defender for IoT now protects industrial IoT, Operational Technology (OT), and building management systems (BMS) with the integration of CyberX’s agentless capabilities for securing unmanaged devices acquired in June.
Our cross-domain detection and response capabilities from Microsoft Defender are deeply integrated with our cloud-native SIEM, Azure Sentinel, reducing complexity and increasing visibility so that defenders see what matters when it matters. In Azure Sentinel we are announcing:
- Improvements to threat intelligence management and new integrations with threat intelligence partners, including the ability to search, add, and track threat indicators, perform TI look-ups, and enrichments as well as creating watchlists for hunting threats—so you can catch more threats, faster.
- User and entity behavior analytics that help SecOps detect unknown threats and anomalous behavior of compromised users and insider threats. New insights are unlocked with user and entity behavior profiles that leverage machine learning and Microsoft’s security research.
- To help Microsoft 365 E5 customers modernize faster, we are offering promotional pricing that will save the typical 3,500 seat deployment $1,500 per month—for a limited time, beginning in November 2020.
ASOS, a leading online fashion retailer, is using Azure Sentinel to detect attacks even while their security team is working remotely during the pandemic.

“With everything running through Azure Sentinel, we’ve reduced the time spent on case management and resolution of alerts by approximately 50 percent.” said Stuart Gregg, Cyber Security Operations Lead, ASOS.
In addition to the XDR and SIEM news, we are enhancing security posture management in Azure Security Center with support for multi-cloud. Now you can see all your Azure, AWS, and GCP security posture in a unified experience within Azure Security Center. Learn more about today’s Azure security announcements here.
Compliance, simplified
Our compliance cloud solutions help customers more easily navigate today’s biggest risks, from managing data or finding insider threats to dealing with legal issues or even addressing standards and regulations. We’ve listened to customers and invested heavily in a set of solutions to help them modernize and keep pace with the evolving and complex compliance and risk management challenges they face.
- One of our key investment areas is the set of Data Loss Prevention products in Microsoft 365. We recently announced the public preview of Microsoft Endpoint Data Loss Prevention (DLP), which means customers can now identify and protect data on devices. Today, we are announcing the public preview of integration between Microsoft Cloud App Security and Microsoft Information Protection, which extends Microsoft’s data loss prevention (DLP) policy enforcement framework to third-party cloud apps—such as Dropbox, Box, Google Drive, Webex, and more—for a consistent and seamless compliance experience
- Customers struggle to keep up with the constantly changing regulations around data protection. To help ease this challenge, we are excited to announce the general availability of Compliance Manager to help businesses simplify compliance and reduce risk by translating complex regulatory requirements to specific controls and through compliance score, get a quantifiable measure of compliance.

Customers like Frost Bank have found that tracking their compliance score makes compliance easier.
“Compliance is a really interesting field. Typically, you have somebody with a legal background, a risk background, or a security background, but very little technical background. And so trying to translate a regulation so that it fits within a technical environment is very difficult. With Compliance Manager, it actually allowed a lot of the tech talk to be translated for the side, the business side, but it also allowed a lot of the business side to be translated to the tech side. For us, it made the conversation very simple and it made the process almost seamless,” said Edward Contreras, CISO, EVP, Frost Bank.
The power of modern cloud-based identity protection
Nothing has done more to simplify the security challenges of remote work during the pandemic than modern identity solutions and Zero Trust architectures. A July 2020 Microsoft poll found that 94 percent of business leaders have already embarked on a Zero Trust journey. Identity is central to simplifying security today and shaping the next generation of the modern security infrastructure.
Microsoft is pushing the frontier of identity through the introduction of a decentralized model built on open standards to help balance the power between individuals and organizations in ways that enhance digital trust while protecting the privacy and reducing the risk of losing personal data.
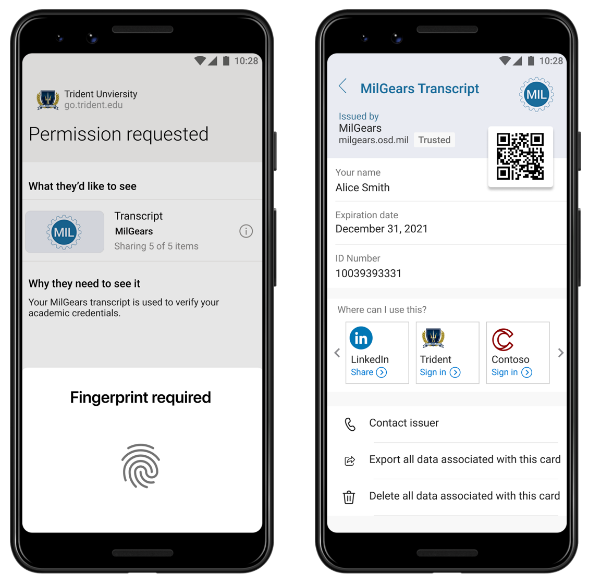
- Today we are announcing a decentralized identity pilot together with the MilGears educational program of the US Department of Defense and Trident at AIU, which helps military veterans and service members enroll in higher education and jumpstart their civilian career.
This technology will significantly reduce the time and effort it takes for veterans to verify their service records and transcripts with universities and employers. It will also help veterans maintain control of their information.
The simplest way to manage identities and embark on a Zero Trust journey today is with Azure Active Directory (AD)—
- Today we are delivering more Azure AD innovation to help customers provide secure remote access to virtually all applications for employees, customers, and partners.

No company or industry is immune to attack and everyone deserves modern protection. The Little Potato Company is a family-owned business with 400 employees headquartered in Alberta, Canada that uses Conditional Access as a critical component in its Zero Trust security strategy. The Little Potato Company recently saw the value of Zero Trust security firsthand when a user’s credentials were compromised and used to attempt to access corporate data. Luckily, the company had deployed Azure AD and Conditional Access, which quickly identified and blocked the login attempts from multiple locations and an unfamiliar operating system.
What you can do today
Security is a journey, and we believe in progress over perfection. The key is that every step you take in the process makes your organization safer and simpler. In fact, it makes all of us safer as we work together to stop malicious activity from causing harm and to protect data and privacy in a modern, connected world.
Here are four things you can do today to make your organization safer and more resilient:
- Use multi-factor authentication. Move toward passwordless.
- Have a plan for keeping software up to date and patch, patch, patch!
- Get a handle on all devices connecting to your network, from phones and laptops to edge devices, and how you’re detecting potential threats to all of them.
- Use benchmarks and insights like Microsoft Secure Score and Compliance Manager to understand your posture and track your progress.
2020 is marking a moment in time that none of us could have imagined; a moment that has amplified the need for a resilient response to unexpected change, and a moment in which digital safety is paramount to productivity and the peace of mind we all need to be at our best. We’re inspired by the way customers are using technology to turn obstacles into innovation, to turn ideas into solutions, and to embrace today’s challenges as an opportunity to build a better, safer world for all. That’s why we at Microsoft are reimagining security, identity, and compliance—





.jpeg)
Comments
Post a Comment